Protect your company’s security with GDS custom-designed managed solutions.
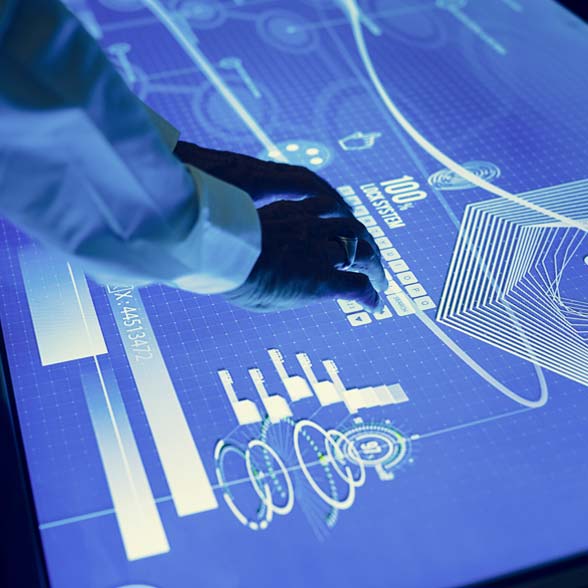
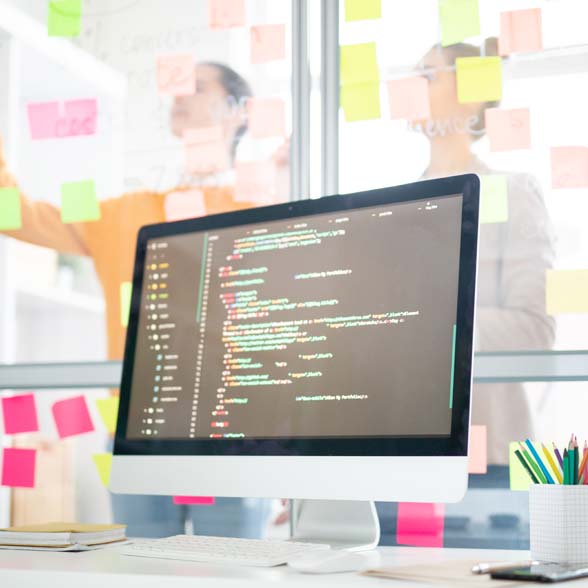
To ensure continuous activity throughout all business operations, every enterprise needs to guarantee complete security of their assets. A personalized security management approach by GDS allows automation and sustainability in data protection, and security demands to be located in one place. Our custom-designed managed solutions also allow us to integrate into any existing infrastructure, and serve all market demands from the smallest to largest businesses.
To ensure continuous activity throughout all business operations, every enterprise needs to guarantee complete security of their assets. A personalized security management approach by GDS allows automation and sustainability in data protection, and security demands to be located in one place. Our custom-designed managed solutions also allow us to integrate into any existing infrastructure, and serve all market demands from the smallest to largest businesses.